
THE SITUATION
Drone technology has advanced dramatically in recent years, with greater usability promoting greater usage. Within the next five years, the drone market is expected to double in size, which will continue to make the technology more accessible to the general public. Additionally, the amount of drone sightings and incidents in restricted airspaces is expected to increase at the same rate.
Drones interfering with air traffic pose a serious threat not only to passengers and pilots, but also to the financial situations of airports and airlines. A notable incident is the drone activity at London Gatwick Airport in December 2018, where approximately 1000 flights were cancelled, and 140,000 passengers had to change their travel plans on account of drones that were sighted and unable to be removed from the airport. It has been estimated that those 36 hours cost the airport and airlines a catastrophic £50 million.
It is not a foregone conclusion that every airport is going to experience a worst-case scenario like that in Gatwick. Since an Anti-Drone System is a costly investment, its procurement needs to be justified by a solid business case. Objective market intelligence is scarce with vendors and systems, as most available information comes in the form of subjective marketing published by vendors.
THE TASK
Airports need a neutral evaluation of drone-related risks and a thorough analysis of technology- and procedural-driven counter measures. The evaluation must be open and unbiased, without any marketing or sales ideas in mind. As drone and counter drone technology are both young and emerging technologies, most airports and local authorities are not yet fully prepared for future developments and potential incidents.
In order to analyze the need for an Anti-Drone System at your airport, various factors must be considered, including:
- Regulatory Framework: Depending on the country your airport is located in, different laws and regulations apply for the operation of Anti-Drone Technology. In many countries the legislation regarding this technology is still in its infancy, leading to legal gray areas and a state of uncertainty on the side of airports and authorities.
- Local Conditions: The risk of drone incidents varies greatly between regions. Local trends and forecasts for drone usage must be analyzed to make a reasonable decision regarding the procurement of an Anti-Drone System. If a system shall be procured, local conditions must be considered as some technological options might be more favorable than others in your specific case. Identifying the best mix of technologies and their optimal dimensioning is one of the key success factors when procuring an Anti-Drone System.
- Future Trends: Drone-related risks must not only be evaluated for today, but also for the near and far future. Therefore, it is essential to consider market forecasts for private and commercial drone usage when analyzing the need or defining the requirements for an Anti-Drone System.
- Types of Procurement: Vendors offer different types of procurement, mainly buying or renting their systems. Airports must carefully decide which option is the best solution for them. Besides the pure investment and operating costs, other factors like flexibility, long-term commitment, strategic partnerships and vendor reputation must be considered.
HOW WE HELPED OUR CLIENTS
With M2P, clients get access to our industry benchmarks, IT market intelligence, and business acumen. Our industry benchmarks help our clients further justify technology capabilities to be pursued by highlighting what other comparable organizations already have, are pursuing, and/or are preparing, either to advance a strategic priority or to be compliant. Our IT market intelligence helps our clients understand what is technically possible from technology promoted by the market, what infrastructure is required to support it, and where the market’s research and investment efforts are most concentrated in addressing future opportunities. Our business acumen helps our clients strengthen their case for pursuing technologies through consideration of other use cases that can also benefit from the same technology.
OUR APPROACH
We provide all the information you need in order to decide whether your airport needs an Anti-Drone System within the near future. Our recommendation will be based on a set of comprehensible, clearly defined deliverables:
- An evaluation of the regulatory situation regarding Anti-Drone Technology within your country and state.
- An analysis of future trends in drone usage within your region, based on a well-established statistical model, applied to your airport‘s specific parameters as well as the results of our data analysis tools.
- An individual risk assessment, based on M2P’s Security Risk Assessment methodology, with a special focus on drone-related threats (see below).
- A detailed business case that compares the cost of an Anti-Drone System with the expected damage it prevents. Additionally, we display which premiums are necessary to reach higher levels of security.
- An evaluation of different technological options and a recommendation which mix of technologies is the most suitable for your airport.
THE SECURITY RISK ASSESSMENT FRAMEWORK
M2P’s Security Risk Assessment Framework aims to provide a detailed list of threats that are not sufficiently covered in the airport’s security concepts and recommends a set of counter measures that should be implemented to close the gap between the airport’s current and desired level of security.
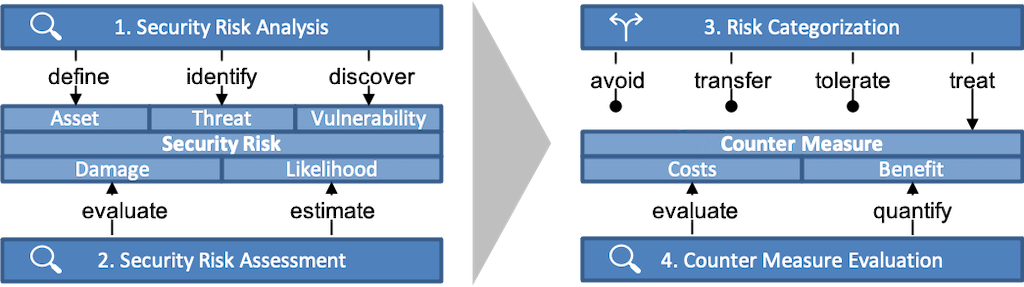
The frameworks operates in four sequential steps:
- Security Risk Analysis: The goal of this step is to create a comprehensive list of risks that are worth evaluating. At first, all assets that need protection are defined. These might be physical objects (e.g., aircrafts), certain places (e.g., terminal or apron areas), people (e.g., passengers or employees) and abstract assets (e.g., sensitive data). After defining these assets, all corresponding threats, that means events that might harm an asset in any way, are identified. Finally, vulnerabilities are discovered by checking for every potential threat whether it is fully covered by an already implemented counter measure. If this is not the case, the considered threat does result in a risk for the airport and will be further evaluated in the next step.
- Security Risk Assessment: This step assess all risks that were identified in the previous step. Therefore, all risks are classified in two dimensions: potential damage and likelihood of occurrence. The potential damage is evaluated mainly based upon similar incidents which occurred in the past (e.g., the Gatwick Drone incident). For estimating the likelihood of occurrence, state-of-the-art data analysis tools and methods are used. Exemplary, in the case of drone threats, a statistical model will be fed with airport specific parameters as well as M2P’s market intelligence data.
- Risk Categorization: Depending on where a risk was in the risk assessment matrix and the availability of technological and organizational options to counter it, risks are now sorted into one of four possible categories. Some risks can be completely avoided by changing operational procedures, some (especially those with very small likelihood of occurrence) can be transferred, e.g., by taking out an insurance, and others can be tolerated because of their low potential damage. All remaining risks must be treated by implementing suitable counter measures.
- Counter Measure Evaluation: The last step of the framework aims to find to most efficient counter measures in order to reach the desired level of security. Every potential counter measure is evaluated regarding their costs and benefits, providing information to support decision making between different risk mitigating options. As different options correspond to different levels of security, having all the available information at hand is key to reach the most economical decisions regarding the security at your airport.
LET’S TALK
We welcome a no obligation discussion on how your airport can stay safe against future risks and threats.
M2P also offers support for RFP-creation, vendor selection, system implementation and many other security-related services.




